XYO ETHDenver Challenges
We are excited to be part of ETHDenver
We are even more excited to meet you all as you look to work with XYO and our suite of products
For ETHDenver we are hosting two $500 bounties for either the best User Interface or a thorough security review.
A few things to consider
- It would be wise before you start to develop your contracts in a local environment. We have some resources for you to get started.
- Don't rush to code, you have some time to think this problem through. In fact, it's far more effective to fully understand the challenge and whiteboarding/brainstorming through the problem before writing
pragma solidity... - Have fun and ask questions!
Pre-requisites
- Web3 working knowledge
- Use dApper - required
- Use dApploy - required
- Use the kovan-testnet. If you need KEth for the testnet, click on this link
- React skills
- We recommend following our style guide
The Challenges
Preparing Your Build Environment
Note For any of these challenges you will need to access our Simple Consensus Smart Contract Dapp Library (SCSC) here and have the kovan testnet ready
Build your environment to be ready to test your solutions:
XYO SCSC Repository -- Smart Contracts available:
- XyPayOnDelivery
- XyStakingModel
- XyStakingConsensus
- XyStakableToken
- XyGovernance
- XyNodeMapping
- PLCR Voting
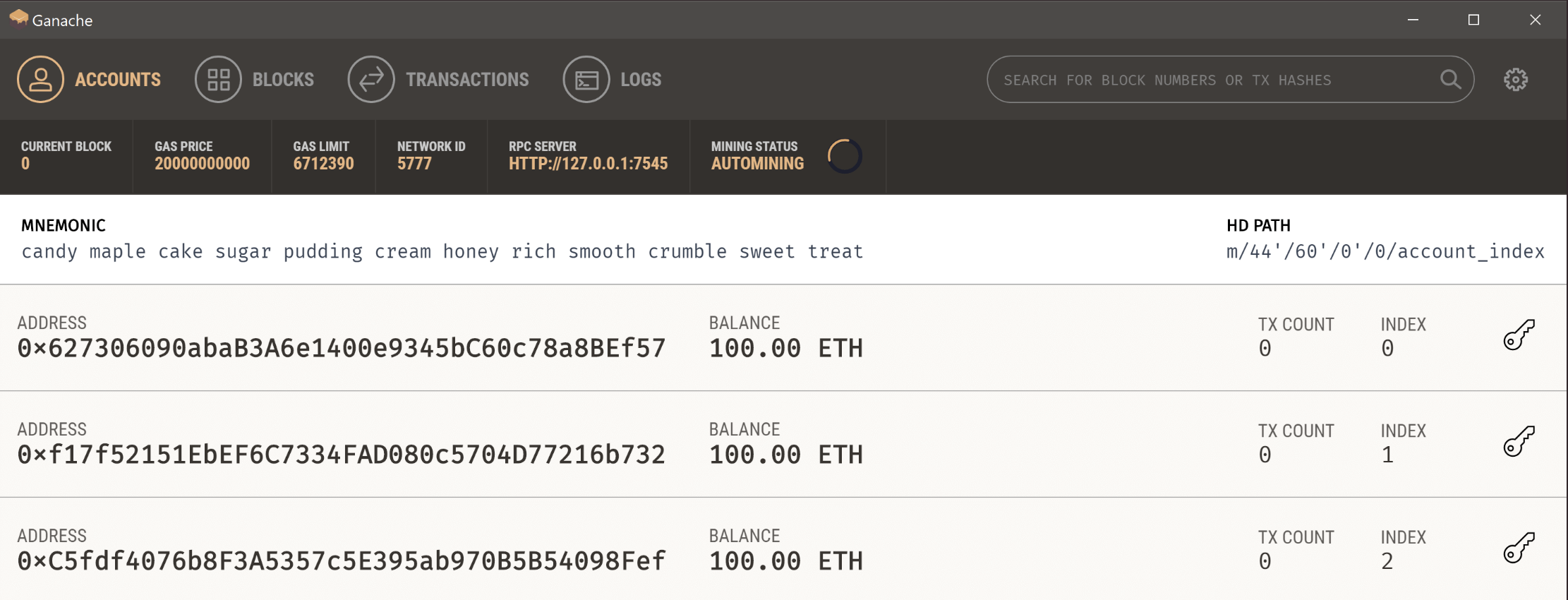
Ganache
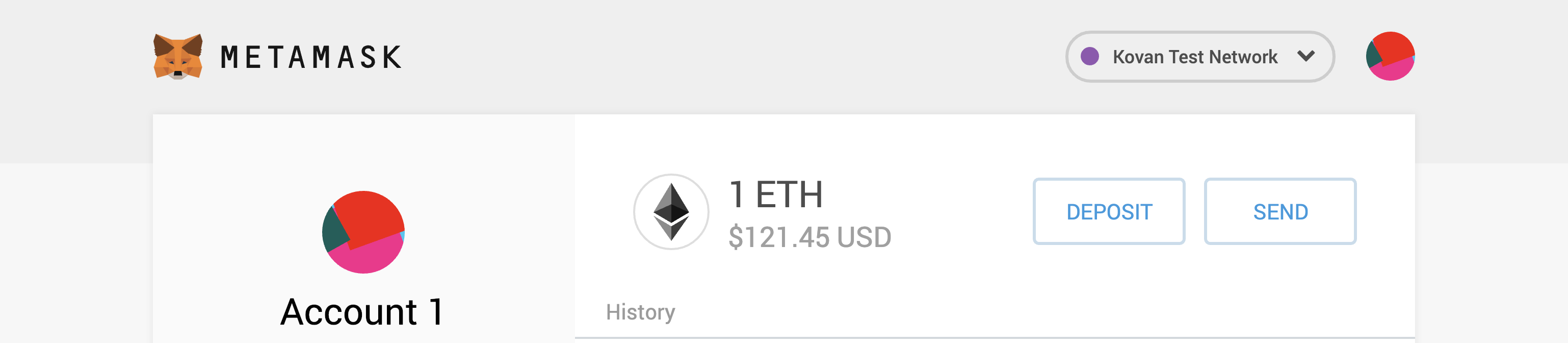
Metamask - pointing to Kovan Testnet
XYO Toolset
Build a User Interface (choose one)
Onboard a Diviner - how can we get an XYO Diviner responding to questions on a testnet away from local development? Make sure you follow the SDK NodeJS Package and it would be helpful to follow the Payable on Delivery Demo Prior to figuring out an onboarding process.
Stake/unstake/withdraw/activate a Diviner - In order for any component on XYO to participate, especially the Diviner, needs to put a stake in (Proof of Stake) to legitimize their responses on-chain. How would you approach this?
Governance - In order for fair rewards upon successful completion of an question/response session, we need to provide rewards from the stake pool. Write and implement a smart contract for voting on re-parameterization of XYO and one time actions.
Withdraw rewards - Write and implement a smart contract that can ask for a widthdraw from a 'master wallet' which holds the totals of successful question/response sessions. Do this without any reentrancy and ensure that the contract is secure and modular, and implements or knows about consensus.
Submit Requests {Pool} - This pool will be holding all total active stake. How, using an assumed governance with staking model would you submit a request to/from the pool? This may look like an interface that can stake, activate, unstake, and withdraw on XYO components.
Submitting your User Interface
We will have more specific instructions prior to the start of the hackathon
- Send your GitHub repo link
- Send the link to your deployed user interface
Security Review
Pour through our smart contracts and conduct a thorough security review
Challenges
- Identify possible exploits and threats in our smart contracts.
- Specifically identify vulnerabilities in our scsc architecture, including coding and logic errors.
- Create echidna fuzz tests with assertions.
Tools to use for this project
Manticore Manticore is a symbolic execution tool for analysis of smart contracts and binaries. Read the docs here We recommend that you take the time to look into the docs to help you or your team create custom analyses You can also start by using the CLI to explore the smart contract library Requirements for use:
- Working knowledge of Python (specifically Python 3.6+)
- Working knowledge of Solidity
- Working knowledge of Docker
echinda Echidna is a Haskell library designed for fuzzing/property-based testing of EVM code. Read the docs here We recommend that you take the time to look into the docs to help you or your team create contracts with tests There is an example contract with tests in the repo The challenge in working with this library is the API to build custom fuzzing systems. Consider the following when considering using this tool:
- There are many configuration options
- The API changes quickly and is poorly documented With this in mind, we strongly recommend you use the examples directory that is provided for you as well as the Trail of Bits Blog
Requirements for use:
- Working knowledge of Haskell
- Working knowledge of Solidity
- Experience with fuzz testing
- Working knowledge of Docker
Submitting your security review
Use GitHub
- Fork the SCSC Library
- Create a pull request and comment your findings from testing
- Make sure to commit message on the pull request - "ETHDenver XYO Security Review"